
Excess Access
Overly permissive access
Users often receive broader permissions than required by role and risk.
Engineering Services
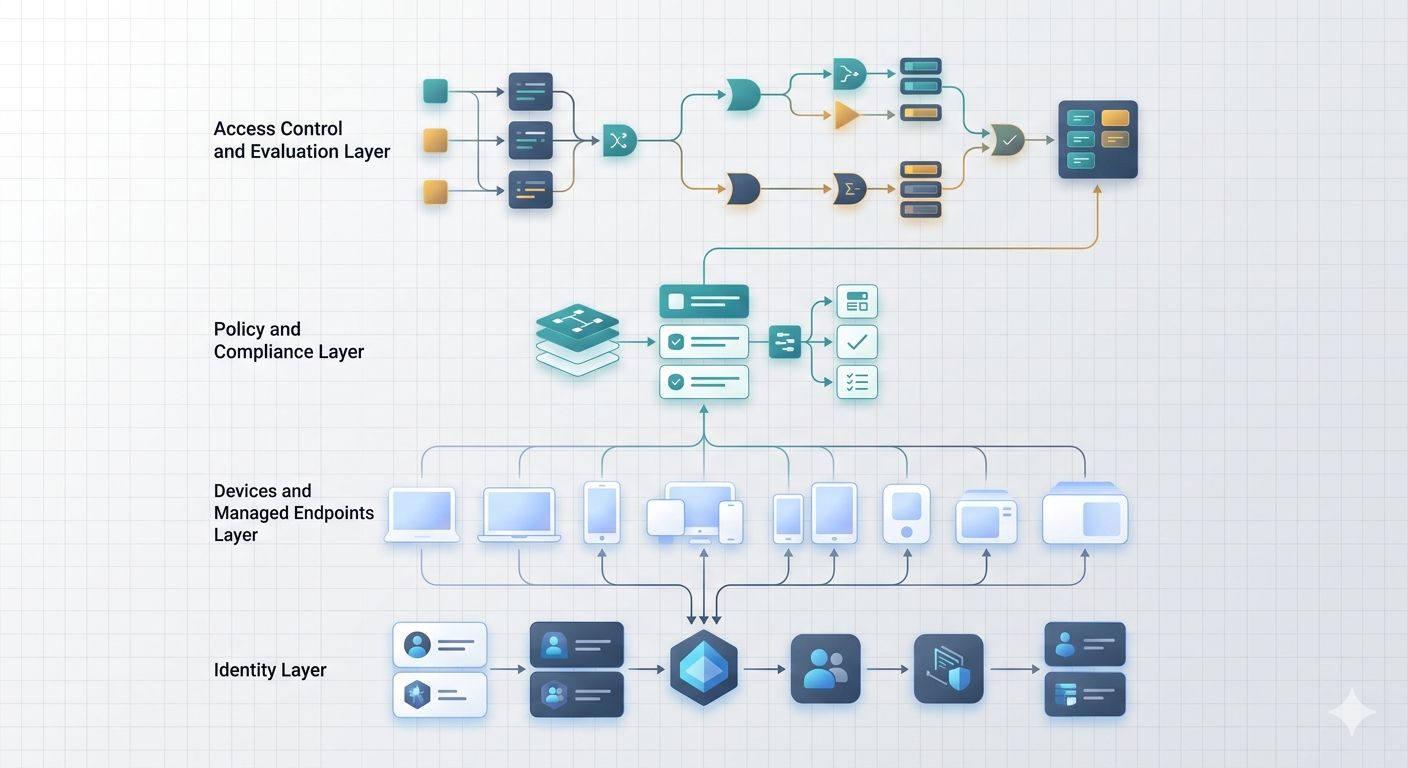
Identity is now the primary security boundary in modern enterprise environments. We design Zero Trust identity architectures that verify users, devices, and applications before access to corporate resources is granted.
We deliver Conditional Access architecture, passwordless authentication strategy, and device trust integration for practical enterprise operations.
With cloud services, remote work, and mobile endpoints, network perimeter controls are no longer the primary security boundary.
Identity must become the central control point. Without structured identity architecture, access policies become inconsistent, credential risk increases, and device trust is weakly enforced.

Excess Access
Users often receive broader permissions than required by role and risk.

Credential Risk
Password-dependent access remains vulnerable to compromise and reuse attacks.

Policy Drift
Access decisions are not consistently enforced across users, apps, and device states.

Device Trust Gap
Applications may grant access without validating endpoint compliance and risk posture.
Design Conditional Access policy sets aligned with security and operational requirements.
Deploy modern authentication methods including biometrics and hardware-backed credentials.
Enforce managed and compliant device requirements before application access.
Zero Trust succeeds when identity, device posture, protection, and monitoring are designed as connected controls instead of isolated settings.
These are the core delivery areas we align to build enforceable identity security architectures inside Microsoft environments.
Define role-based access controls and identity lifecycle operations.
Integrate identity protection controls with Defender security capabilities.
Provide visibility into authentication activity and identity security events.
Together, these deliverables give the team a practical foundation for running Zero Trust identity architecture after the project work is complete.
Zero Trust identity architecture depends on a platform model that connects policy, identity, operations, and governance rather than optimizing one layer at a time. These are the areas we usually align first so the foundation can scale cleanly.
Identity platform for authentication, authorization, and governance controls.
Context-based policy enforcement using risk, device state, and access context.
Detect risky sign-ins and signals of credential compromise.
Implement stronger user verification without reusable passwords.
Secure administrative access through role and privilege governance.
Connect identity controls with device trust and endpoint protection systems. Related: /intune-device-management
That alignment turns Zero Trust identity architecture into a workable platform strategy instead of a set of disconnected configuration decisions.
Our approach to Zero Trust identity architecture is designed to reduce delivery risk while keeping decisions grounded in the operating reality of the environment. Each step moves from assessment into design, implementation, and handoff so the solution is easier to run after launch.
Review authentication methods, access policies, and current risk posture.
Define Conditional Access model, authentication strategy, and control boundaries.
Deploy identity security policies and governance controls in phased rollout.
Align device compliance posture with identity-driven access enforcement.
Implement identity telemetry, threat detection, and response procedures.
That sequence keeps Zero Trust identity architecture practical to deliver, controlled during rollout, and sustainable once it moves into day-two operations.
Scenario
Secure remote application access with Conditional Access enforcement and identity protection monitoring.
Scenario
Administrative role protection, privileged access workflows, and secure admin authentication controls.
Scenario
Application-specific policies with device compliance checks and adaptive authentication controls.
Scenario
Credential compromise detection, risk-based access control, and identity threat monitoring.
Zero Trust identity architecture works best when the core design decisions behind this section are planned together instead of being handled as isolated tasks. These are the areas we typically define first so the solution is easier to deploy, govern, and support over time.
Identity security implemented as part of enterprise architecture, not isolated controls.
Deep delivery experience across Entra ID, Intune, and Defender services.
Security controls designed for real operational environments and supportability.
Identity verification and device trust are engineered together for stronger access control.
When these areas are aligned, Zero Trust identity architecture becomes easier to operate, measure, and improve without adding avoidable complexity for the team.

Zero Trust succeeds when identity, device posture, application access, session risk, and exception handling are designed as one decision model.
That requires more than turning on controls. It requires a clear operating pattern for how trust is granted and reviewed.
Identity policy becomes stronger when device compliance, app protection, role boundaries, and governance evidence are aligned.
The section uses one security visual to explain the recurring signals that keep identity-led trust decisions from becoming static policy.
Identity, endpoint trust, application access, and governance evidence managed as one Zero Trust operating model.
Authentication strength, role context, and access policy are reviewed with real operational ownership.
Compliance, enrollment, risk, and platform state reinforce Conditional Access rather than sitting in another workstream.
Exceptions, reviews, and evidence help teams defend why access is allowed, denied, or changed.
Engagement
Outcome: clear roadmap for identity security improvements.
Engagement
Outcome: production-ready Zero Trust identity platform.
Engagement
Outcome: mature identity security operations.
Zero Trust is a model where access to systems is continuously verified based on identity, device posture, and contextual risk.
Identity is now the primary security boundary in modern cloud-based enterprise environments.
Conditional Access enforces policy controls before granting access to applications.
Passwordless authentication replaces traditional passwords with stronger user verification methods.
If your identity security architecture has evolved organically, we can design a structured Zero Trust framework for your environment.